CLOUD PLATFORM SECURITY: PROTECT YOUR DIGITAL WORKSPACE
As your business migrates to the cloud, your security must evolve with it.
The shift to remote work and cloud collaboration has fundamentally changed how organizations operate. While cloud platforms enable unprecedented flexibility and productivity, they also create new security challenges that traditional approaches fail to address. Meet Me In The Cloud delivers comprehensive cloud security solutions that protect your digital environment across all platforms, devices, and locations.
Partnering with industry leaders like Cisco, FireEye, and Sophos, we implement best-in-class security technologies customized to your specific requirements—creating a robust security foundation that enables confident collaboration rather than restricting it.
COMPREHENSIVE PROTECTION:
SECURING EVERY ASPECT OF YOUR CLOUD ENVIRONMENT
Layered security designed for today’s distributed workplace
SECURITY AWARENESS TRAINING
Transform your greatest vulnerability into your strongest defense
Human error accounts for nearly all successful cyber attacks, making your employees simultaneously your greatest vulnerability and your most important defense. Our comprehensive security awareness program:
- Phishing Simulation & Training: Teaches employees to identify and avoid increasingly sophisticated social engineering attacks
- Security Best Practices: Builds practical knowledge that reduces risky behaviors
- Threat Recognition: Develops skills to identify suspicious activities before they become breaches
- Incident Reporting: Establishes clear protocols for flagging potential security concerns
By transforming security awareness from occasional training to ongoing culture, we help your team become active participants in your security posture rather than unwitting vulnerabilities.

EMAIL SECURITY & ENCRYPTION
Protect your most targeted communication channel
As the primary entry point for cyberattacks, email requires sophisticated protection. Our comprehensive email security solutions provide:
- Advanced Threat Detection: Identification of sophisticated phishing, malware, and business email compromise attempts
- Data Loss Prevention: Controls that prevent sensitive information from leaving your organization
- Email Encryption: Protection for confidential communications in transit and at rest
- Account Takeover Protection: Detection of compromised email credentials before they can be exploited
These integrated capabilities ensure your email environment—where customer data, financial records, and intellectual property frequently reside—remains protected against increasingly sophisticated threats.
WEB BROWSING & CONTENT SECURITY
Prevent threats before they enter your network
One wrong click can introduce malware that remains undetected for months while exfiltrating data and monitoring traffic. Our web security solutions provide proactive protection:
- Real-Time Content Analysis: Examination of web content before it reaches users
- URL Filtering: Blocking of known malicious websites and suspicious domains
- Application Control: Management of web application access based on business requirements
- Inappropriate Content Filtering: Prevention of policy violations and potential legal issues
This proactive approach stops threats at the perimeter, preventing them from ever reaching your internal systems and data.

DATA LOSS PREVENTION
Safeguard your most valuable information assets
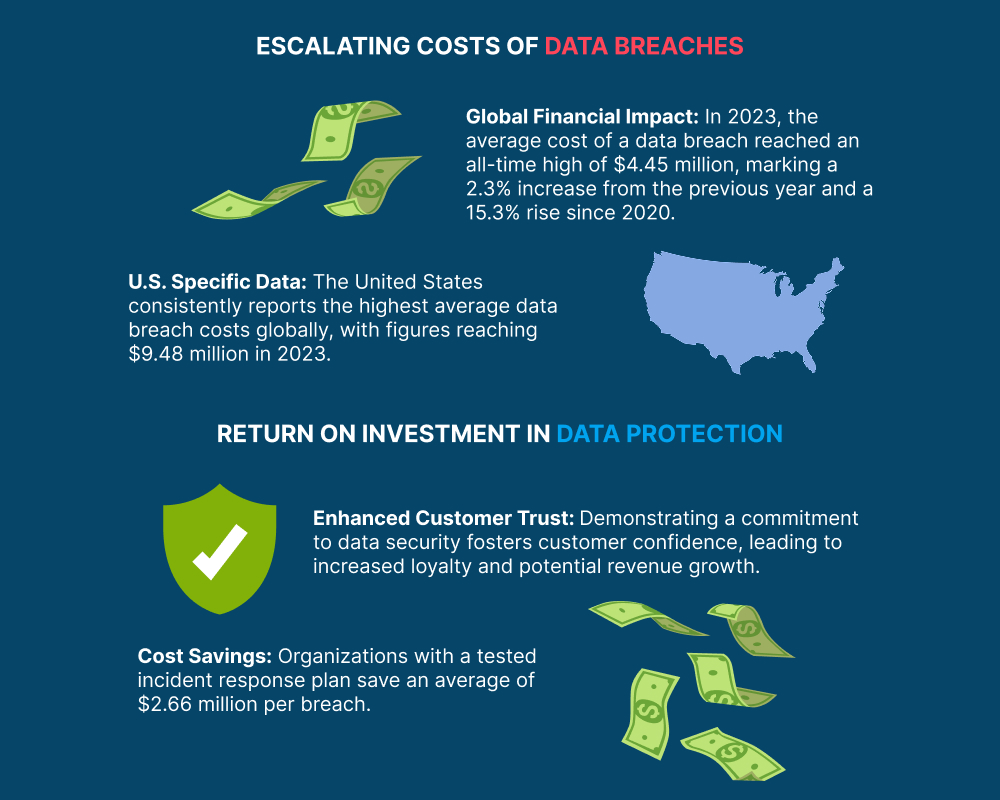
With the 2022 Cost of a Data Breach report placing the average breach cost in the millions, data protection is a business imperative. Our data loss prevention platform:
- Content Inspection: Identifies sensitive data across your environment
- Policy Enforcement: Applies consistent controls based on data classification
- Behavioral Analysis: Detects unusual access patterns that may indicate theft attempts
- Integration Capabilities: Works seamlessly across cloud platforms, endpoints, and networks
Using industry-leading Cisco technology, we implement scalable data protection that integrates with your existing environment in minutes, providing immediate risk reduction.
FILE ACTIVITY MONITORING & PROTECTION
Real-time visibility into your critical data
Traditional audit approaches can’t keep pace with modern threats. Our real-time monitoring capabilities provide:
- User Activity Tracking: Visibility into all file access and modifications, even from privileged users
- Anomaly Detection: Identification of unusual patterns that may indicate compromise
- Immediate Alerting: Real-time notifications of suspicious activities
- Forensic Reporting: Detailed evidence for investigation and compliance purposes
This continuous monitoring enables early detection of potential breaches, allowing you to respond before significant damage occurs.


ENDPOINT SECURITY
Protect every device that accesses your environment
As the attack surface expands with each new device, comprehensive endpoint protection becomes essential:
- Advanced Threat Detection: Identification of known and unknown threats targeting endpoints
- Behavioral Monitoring: Recognition of suspicious activities regardless of signature detection
- Automated Response: Immediate containment of compromised devices
- Cross-Platform Protection: Consistent security across Windows, Mac, Linux, and mobile devices
Our endpoint security solutions combine multiple detection technologies with automated response capabilities to protect devices regardless of location or ownership.
IoT SECURITY & EDUCATION
Secure the expanding universe of connected devices
Every IoT device represents a potential entry point for attackers. Our IoT security solutions provide:
- Network Segmentation: Isolation of IoT devices from critical systems
- Traffic Monitoring: Detection of unusual communications from connected devices
- Vulnerability Management: Identification and remediation of IoT security weaknesses
- Secure Configuration: Implementation of hardened settings for all connected devices
Combined with education on secure IoT deployment, these measures protect your expanding device ecosystem from becoming an attacker’s gateway.


FIREWALL MANAGEMENT & ANTIVIRUS
Your fundamental security foundation
Even with advanced solutions, traditional security controls remain essential:
- Next-Generation Firewall Management: 24/7 monitoring and management of your perimeter defenses
- Advanced Threat Intelligence: Integration of global threat data to block emerging attacks
- AI-Powered Antivirus: Real-time scanning using artificial intelligence and machine learning
- Automated Remediation: Immediate response to detected threats
Our team ensures these foundational security elements remain continuously optimized, updated, and monitored.
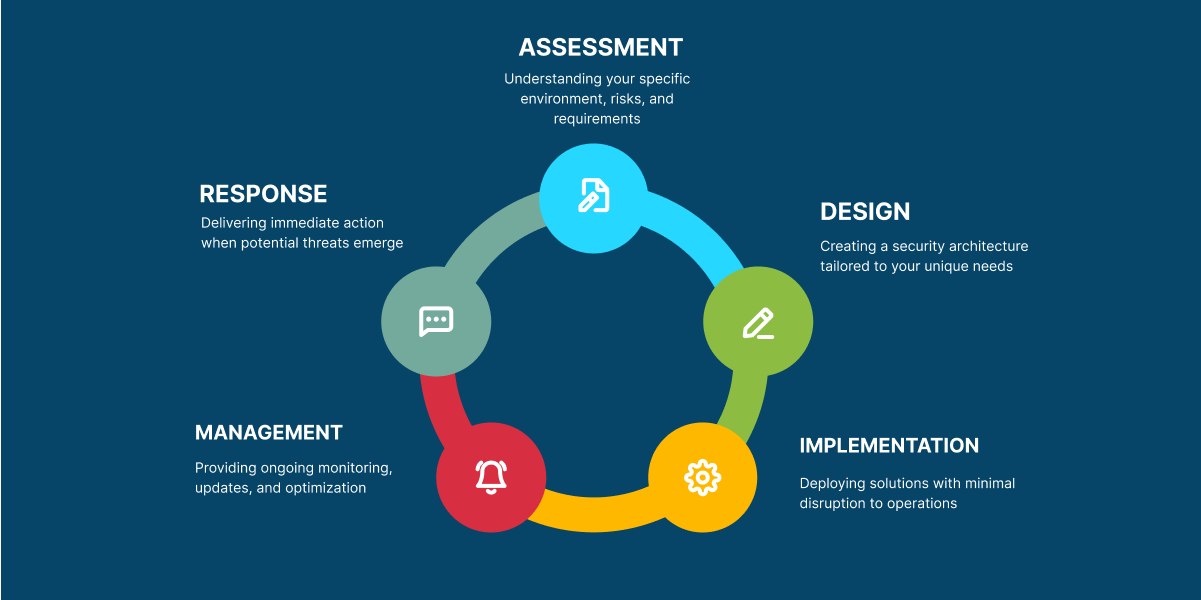
THE MEET ME IN THE CLOUD SECURITY APPROACH
Protection that enables rather than restricts
Unlike security solutions that prioritize control over usability, our approach focuses on enabling secure collaboration. We understand that security must support your business operations, not impede them.
Our security implementation process includes:
SECURE YOUR CLOUD JOURNEY
Whether you’re migrating to cloud platforms, enhancing your virtual event capabilities, or optimizing your existing collaboration environment, Meet Me In The Cloud provides the security expertise and technologies needed to protect your digital workspace.
Our team of cybersecurity experts integrates email security, network security, and cloud security solutions from leading vendors, configuring them specifically for your environment and requirements—transforming security from a concern into a competitive advantage.
